Cybersecurity threats continue to evolve, targeting businesses of all sizes. Choosing the right cybersecurity software is critical to safeguarding sensitive data, networks, endpoints, and cloud environments. With so many options on the market, finding a solution that balances performance, usability, and security can be overwhelming.
This guide highlights the best cybersecurity software of 2025, detailing features, pros, cons, and pricing to help you make an informed choice.
Why Cybersecurity Software Matters
Modern businesses face sophisticated threats, from malware and ransomware to insider attacks and phishing campaigns. Cybersecurity software provides:
- Real-time threat detection to stop attacks before they escalate
- Data protection through encryption and access controls
- Compliance support for regulations like SOC 2 and ISO 27001
- Centralized monitoring across on-premises, cloud, and hybrid environments
- Automated response to reduce downtime and operational disruption
Investing in cybersecurity tools not only mitigates risk but also enhances trust with customers and partners, protects brand reputation, and ensures operational continuity.
Top Cybersecurity Software for 2025
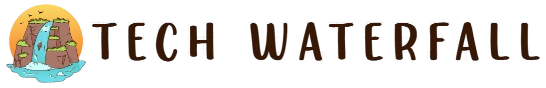
NordLayer – Best for DNS-Level Threat Blocking
Price: From $8/user/month (5-user minimum)
Why Choose NordLayer: NordLayer secures networks with DNS-level threat blocking, preventing harmful websites from reaching devices. Its Zero Trust Network Access (ZTNA) framework and real-time download scanning ensure safe connections for remote employees.
Key Features:
- AES-256 encryption, multi-factor authentication
- Network segmentation and site-to-site VPN
- Centralized control panel and identity management
Pros: Strong access control, zero-trust security
Cons: Complex server setup, limited server locations
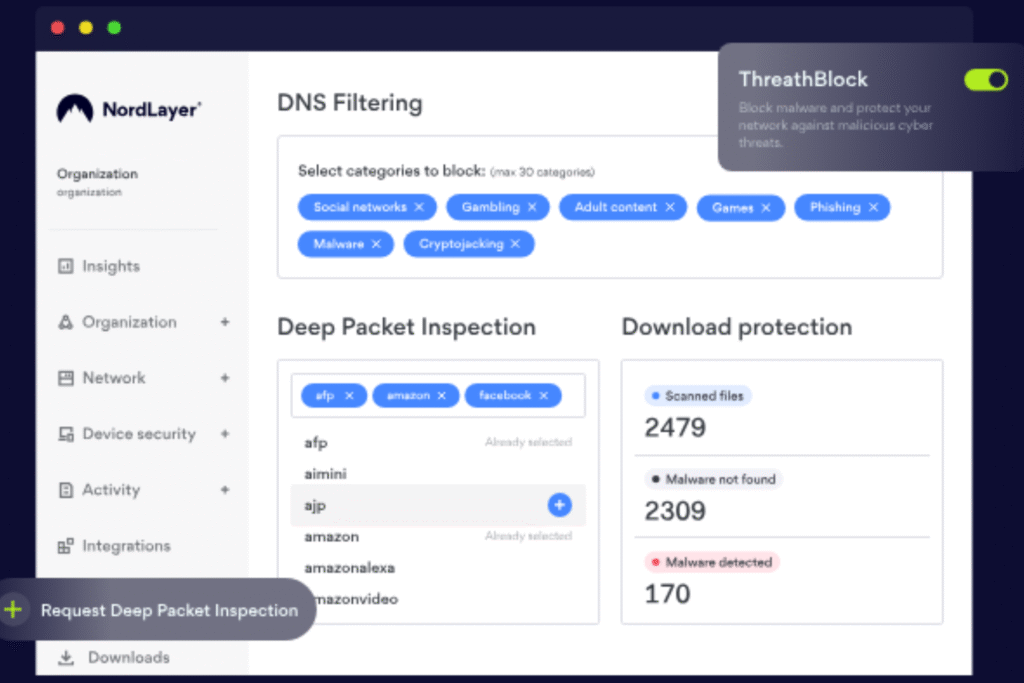
Aikido Security – Best for Code-to-Cloud Protection
Price: From $350/month; free plan available
Aikido Security integrates DevSecOps with cloud security, covering malware detection, container scanning, and infrastructure as code analysis. It prioritizes actionable alerts, reducing noise and focusing on real vulnerabilities.
Key Features:
- Cloud posture management, static code analysis
- Secrets detection, container image scanning
- Compliance support (SOC 2, ISO 27001)
Pros: Scalable, actionable insights, comprehensive dashboards
Cons: Lacks endpoint security and intrusion detection
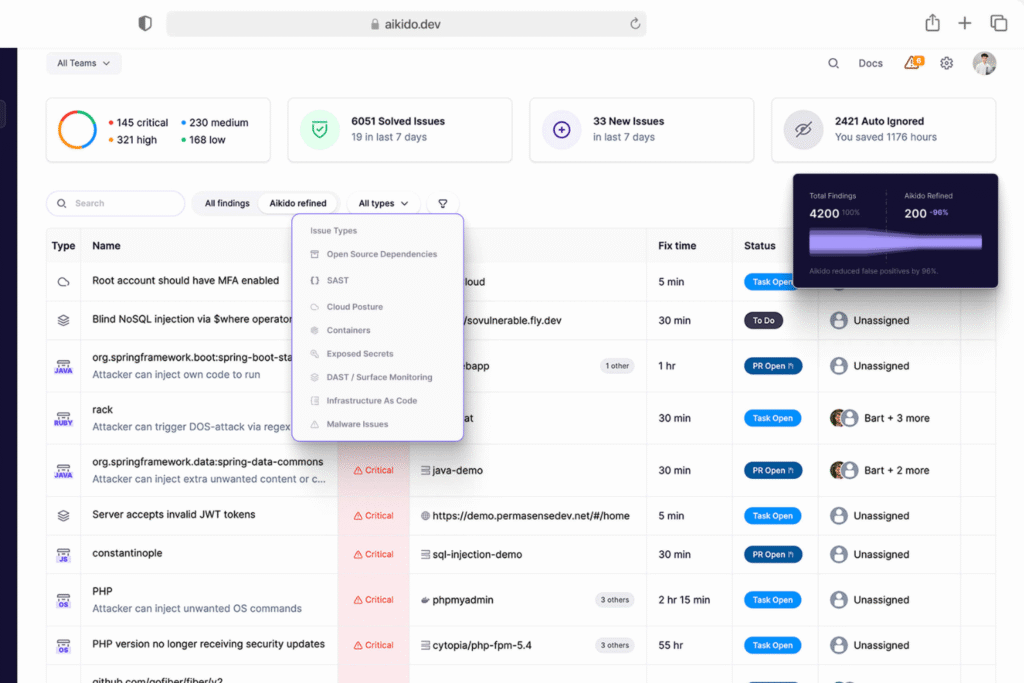
Teramind – Best for Insider Threat Detection
Price: From $19/user/month; free trial available
Teramind monitors user behavior across applications, emails, and file transfers. Rule-based risk analysis and real-time alerts enhance insider threat detection and compliance monitoring.
Key Features:
- Video session recording, remote desktop control
- IT forensics capabilities
- Policy-driven alerting
Pros: Customizable policies, comprehensive monitoring
Cons: Can be complex for small teams
ManageEngine Endpoint Central – Best for IT Infrastructure Management
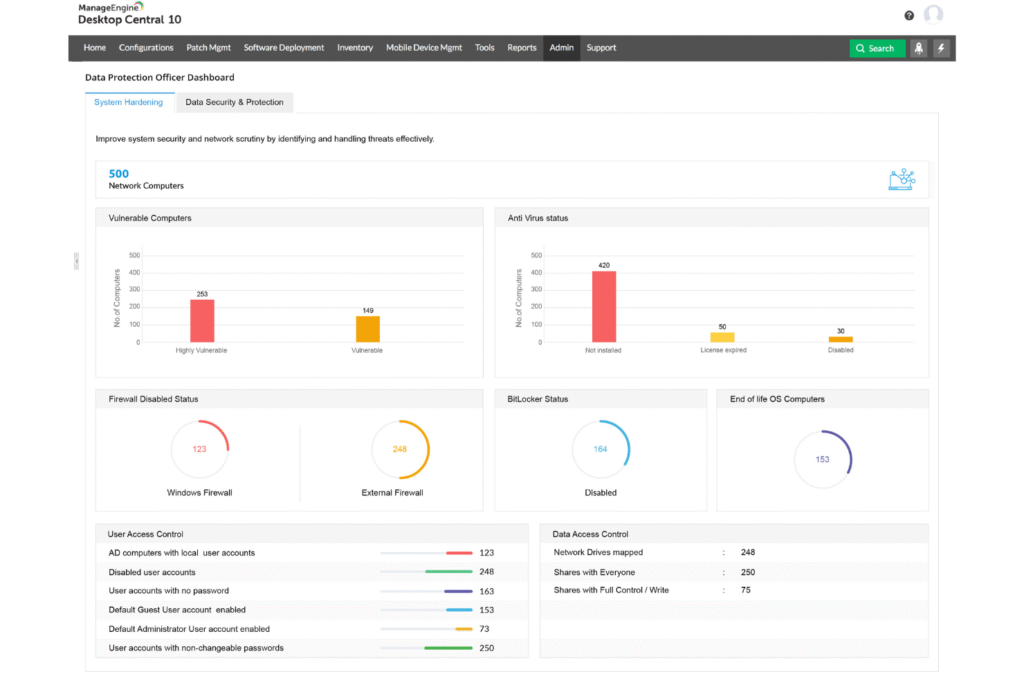
Price: From $10/user/month; free trial available
This platform unifies endpoint management and security, offering automated patching, vulnerability remediation, and centralized control over devices.
Key Features:
- Next-gen antivirus, browser security, application control
- Identity and access management, reporting and auditing
- OS imaging, software deployment
Pros: Extensive customization, consistent patch management
Cons: Steep learning curve, limited mobile device management
ManageEngine Log360 – Best for Integrated DLP and CASB
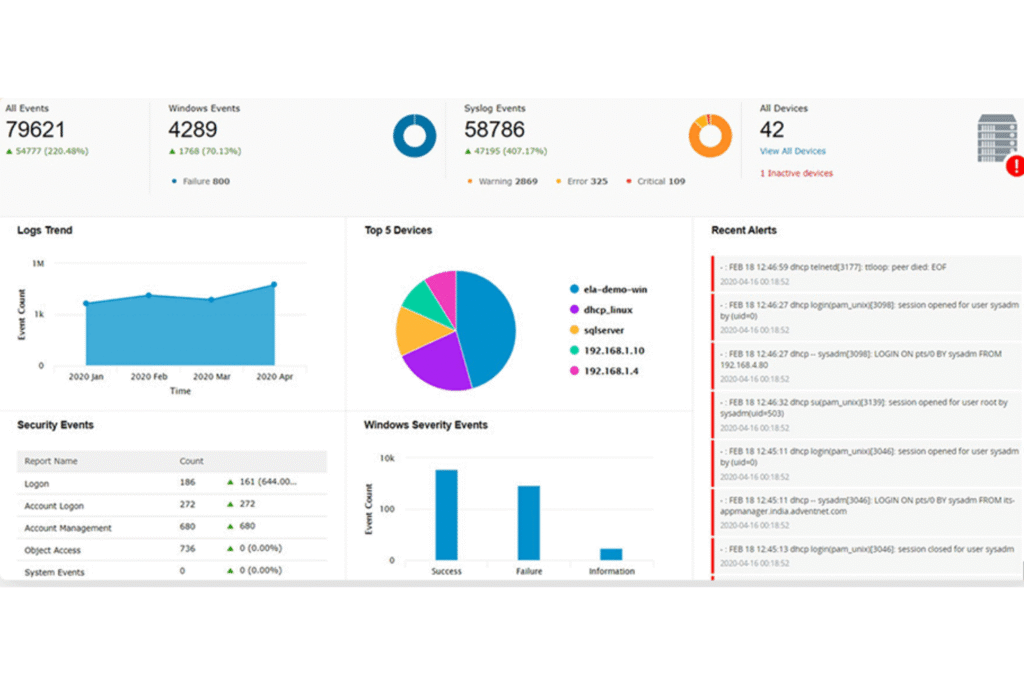
Price: Pricing upon request; free demo available
Log360 combines SIEM, DLP, and CASB functionalities, providing machine learning-based threat detection and real-time analytics across hybrid environments.
Key Features:
- Log management, incident management, user behavior analytics
- Security event correlation, forensic analysis
- Compliance reporting
Pros: Comprehensive threat intelligence, robust analytics
Cons: Complex setup, requires regular maintenance
Malwarebytes – Best Rootkit Scanner

Price: From $49.99/device/year; 60-day money-back guarantee
Malwarebytes excels at detecting rootkits and zero-day threats, offering antivirus, VPN, and anomaly detection for both personal and business devices.
Key Features:
- Automatic system repairs, real-time scanning
- Pre-built integrations with ServiceNow, Slack, and IBM QRadar
Pros: Beginner-friendly, free rootkit scanner
Cons: Some features are Windows-only
ESET PROTECT Complete – Best for Proactive Threat Detection
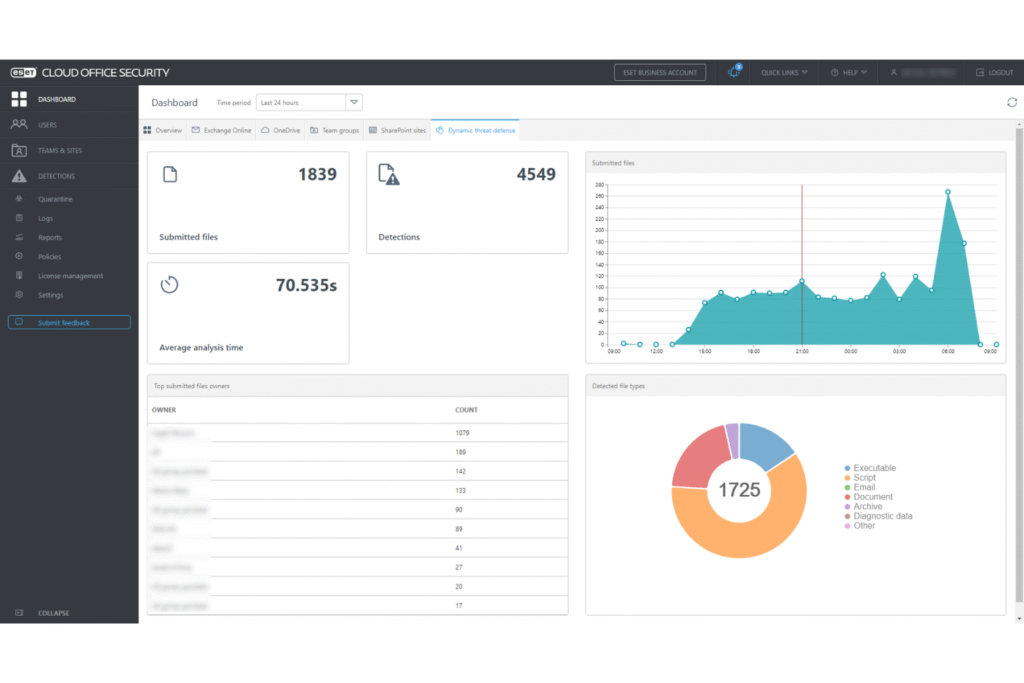
Price: From $338.50/year; 30-day free trial
ESET provides AI-powered threat prevention, endpoint protection, and cloud app security with detailed reporting and a unified management dashboard.
Pros: Comprehensive coverage, remote management
Cons: Can slow devices during scans, costly for some users
Dynatrace – Best for Securing Applications
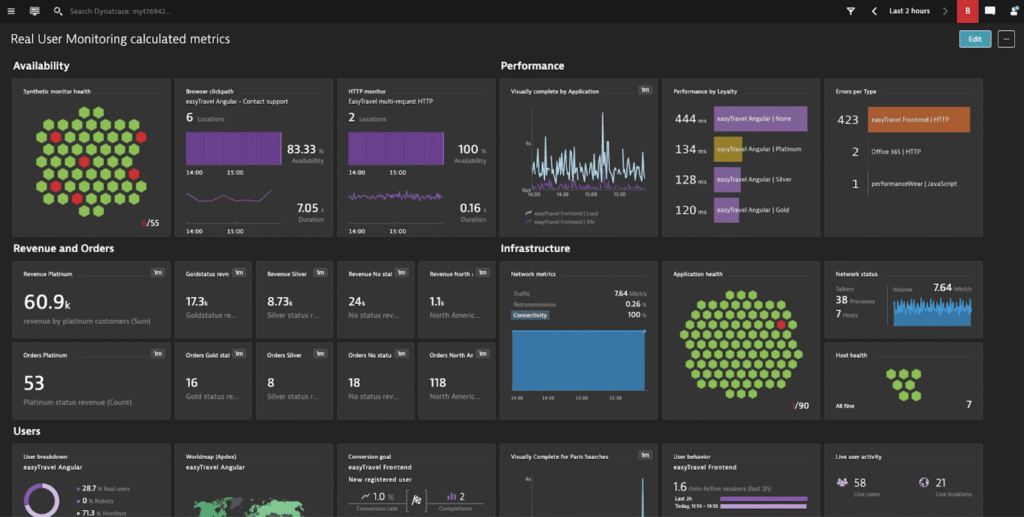
Price: From $0.0001; 15-day free trial
Dynatrace offers automated application monitoring, root-cause analysis, and performance insights, combining security with observability.
Pros: Easy deployment, robust monitoring
Cons: Best suited for enterprise applications, limited support
New Relic – Best for Full-Stack Observability
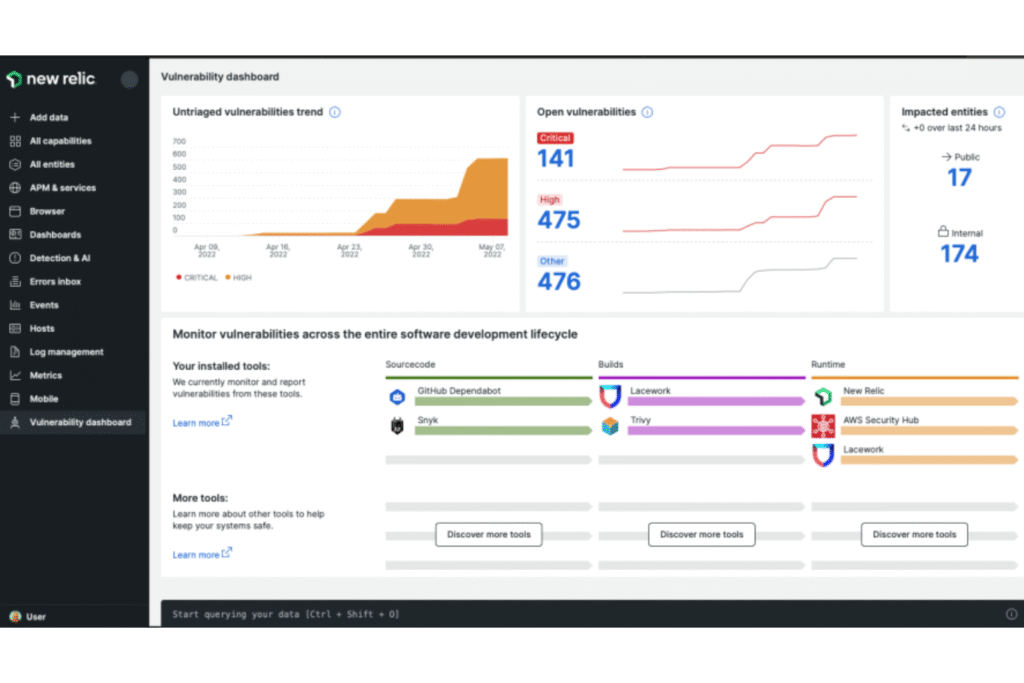
Price: Pricing upon request; free plan available
New Relic provides real-time visibility into applications and infrastructure with vulnerability management and interactive application security testing.
Pros: Holistic tech stack monitoring, AI-powered insights
Cons: Steep learning curve for new users
Datadog – Best for Educational Institutions
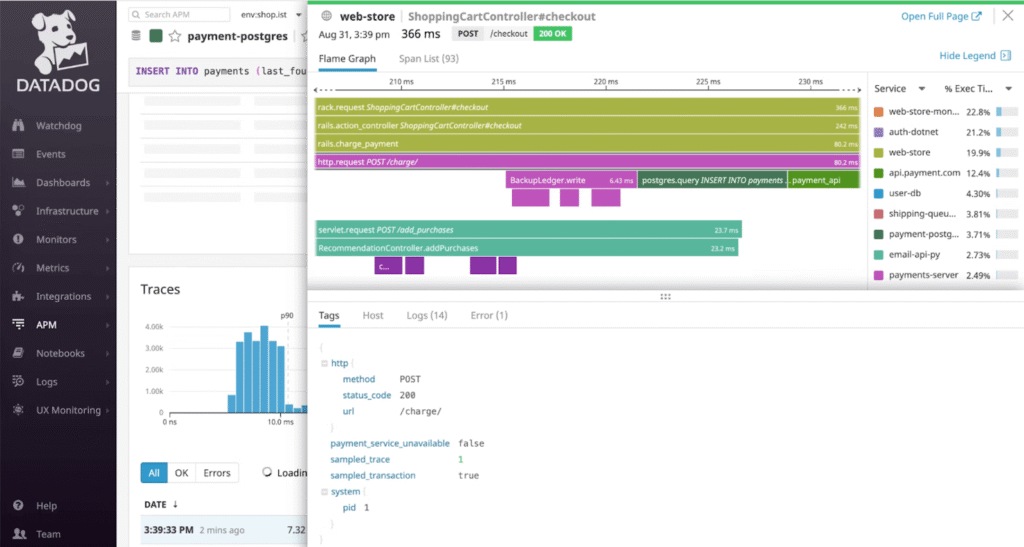
Price: From $15/user/month; 14-day free trial
Datadog ensures compliance and data security with infrastructure monitoring, sensitive data scanning, and real-time alerts for emerging threats.
Pros: Unified monitoring, beginner-friendly dashboards
Cons: Complex private hardware setup, can be expensive
Selection Criteria for Cybersecurity Software
When evaluating cybersecurity tools, consider:
- Core Functionality: Threat protection, data security, compliance, visibility, and incident response.
- Standout Features: Predictive analytics, user behavior monitoring, AI/ML-powered threat detection.
- Usability: Intuitive dashboards and easy navigation for all users.
- Onboarding: Comprehensive tutorials, setup guides, and training materials.
- Customer Support: Responsive teams, community forums, dedicated account managers.
- Value for Money: Scalable features without hidden costs.
- Customer Reviews: Real-world feedback on usability, support, and effectiveness.
Key Features to Look For
- Real-Time Threat Detection: Immediate identification of cyber threats
- Automated Incident Response: Reduces manual intervention and downtime
- Advanced Firewalls: Protects networks from unauthorized access
- Endpoint Security: Safeguards remote and on-site devices
- Encryption & MFA: Protects sensitive data and credentials
- Cloud Security: Ensures multi-cloud and hybrid environment protection
- SIEM & Vulnerability Scanning: Centralized insights and proactive patching
- Data Loss Prevention: Secures critical business information
Benefits of Cybersecurity Software
Enhanced Threat Response: Detect and neutralize threats instantly
- Regulatory Compliance: Meet legal and industry standards
- Data Breach Prevention: Protects sensitive and personal data
- Productivity Maintenance: Reduces downtime caused by attacks
- Brand Trust: Demonstrates commitment to data security
Cybersecurity Software Pricing
| Plan Type | Average Price | Common Features | Best For |
|---|---|---|---|
| Free | $0 | Basic protection, limited features, recommended for personal use or very small businesses | Personal use, very small businesses with minimal online presence |
| Basic | $10 – $30/month | Antivirus, firewall, email security, web filtering | Small businesses with basic security needs, home offices |
| Standard | $30 – $70/month | Basic features plus endpoint protection, mobile security, VPN | Growing businesses, startups, organizations with some sensitive data |
| Premium | $70 – $150/month | Standard features plus advanced threat protection, identity management, security analytics | Mid-sized businesses with expanding security needs, organizations with customer data |
| Enterprise | Custom Pricing | Premium features plus scalability options, dedicated support, BAS software, full-suite solutions | Large enterprises, organizations with complex IT infrastructure, businesses handling highly sensitive data |
Selecting the right plan ensures cost-effective protection without compromising coverage.
2025 Cybersecurity Trends
- Enhanced Endpoint Security: Protects remote devices with zero-trust models
- Cloud Security Enhancements: Better control across multi-cloud and hybrid setups
- Behavioral Analytics: Detect insider threats via user activity monitoring
- Decentralized Security Operations: Blockchain-based approaches for data integrity
- Decline of Signature-Based Antivirus: Behavioral and AI-based detection methods are taking over
Frequently Asked Questions:
What is the best cybersecurity software for small businesses in 2025?
For small businesses, tools like NordLayer, Malwarebytes, and ManageEngine Endpoint Central offer robust protection with affordable pricing and easy deployment.
How do I choose the right cybersecurity software for my organization?
Start by identifying your key security needs, such as endpoint protection, cloud security, or insider threat detection. Consider ease of use, integrations with existing tools, and scalability for future growth.
Are these cybersecurity solutions suitable for remote or hybrid work environments?
Yes. Most of the reviewed tools, including Aikido Security and NordLayer, offer cloud integration, remote monitoring, and zero-trust security to protect distributed teams effectively.
What features should I prioritize in cybersecurity software?
Key features include real-time threat detection, automated incident response, endpoint protection, encryption, multi-factor authentication, and compliance management.
Can these solutions protect against insider threats?
Yes. Tools like Teramind and Aikido Security use user behavior analytics and rule-based monitoring to detect and prevent insider risks.
Do these tools support multi-cloud and hybrid infrastructures?
Many platforms, including ManageEngine Log360 and ESET PROTECT Complete, provide cross-environment visibility and security, covering both cloud and on-premises systems.
Are these cybersecurity solutions beginner-friendly?
Several tools, like Malwarebytes and Datadog, are designed with intuitive dashboards and guided onboarding, making them accessible even for teams with limited IT expertise.
Conclusion
In 2025, cybersecurity is no longer optional—it’s a critical pillar for protecting your business, data, and digital operations. The 20 reviewed solutions, from NordLayer’s DNS-level threat blocking to Teramind’s insider threat detection and ManageEngine’s comprehensive IT management, provide robust protection for organizations of all sizes. Choosing the right cybersecurity software depends on your organization’s specific needs, whether it’s endpoint security, cloud protection, compliance management, or real-time threat detection. By prioritizing tools that offer seamless integration, actionable insights, and scalable features, businesses can strengthen their security posture while maintaining productivity and operational efficiency.